ENS SECURITY POLICY
1. Approval and entry into force
This Information Security Policy is effective from the date of signature and until it is replaced by a new Policy.
2. Misión de Asseco Spain S.A.
In order to achieve its objectives, Asseco Spain assumes its commitment to information security, committing itself to its proper management, in order to offer all its stakeholders the greatest guarantees regarding the security of the information used.
Our mission is to offer high-impact 360° technological solutions and services with a high level of customization
These systems must be managed diligently, taking appropriate measures to protect them against accidental or deliberate damage that may affect the availability, integrity, traceability, authenticity or confidentiality of the information processed or the services provided.
The objective of information security is to guarantee the quality of information and the continuous provision of services, acting preventively, monitoring daily activity and reacting promptly to incidents.
ICT systems must be protected against rapidly evolving threats with the potential to affect each of the dimensions, information and services provided. To defend against these threats, a strategy that adapts to changes in environmental conditions is required to ensure the continuous delivery of services. This implies that departments must apply the minimum security measures required by the National Security Scheme, as well as continuously monitor the levels of service provision, monitor and analyze reported vulnerabilities, and prepare an effective response to incidents to ensure the continuity of the services provided.
Different departments must ensure that ICT security is a part of the
Comprehensive management of each stage of the system’s life cycle, from conception to decommissioning, development or procurement decisions and operating activities. Security requirements and funding needs must be identified, both for the products it develops and their associated services, as well as for the base software purchased from third parties.
Departments must be prepared to prevent, detect, react to and recover from incidents, in accordance with Article 8 of the ENS (Article 8. Prevention, detection, response and conservation).
3. Scope
This policy applies to all the entity’s information systems and to all members of Asseco Spain S.A., involved in Services and Projects aimed at the public sector, which require the application of ENS, without exceptions. That is: the information systems that support the development and maintenance of software According to the current applicability statement
4. Objectives
For all of the above, the Management establishes the following information security objectives:
➔ Provide a framework to increase resilience or resilience for an effective response.
➔ Ensure the rapid and efficient recovery of services, in the face of any physical disaster or contingency that may occur and that could put the continuity of operations at risk.
➔ To prevent information security incidents to the extent technically and economically feasible, as well as to mitigate information security risks generated by our activities.
➔ Guarantee the confidentiality, integrity, availability, authenticity and traceability of the information.
5. Regulatory framework
One of the objectives must be to comply with applicable legal requirements and with any other requirements that we subscribe to in addition to the commitments acquired with customers, as well as the continuous updating of them. To this end, the legal and regulatory framework in which we carry out our activities is:
• REGULATION (EU) 2016/679 OF THE EUROPEAN PARLIAMENT AND OF THE COUNCIL of 27 April 2016 on the protection of natural persons with regard to the processing of personal data and on the free movement of such data.
• Organic Law 3/2018, of 5 December, on the Protection of Personal Data and guarantee of digital rights.
• Royal Legislative Decree 1/1996, of 12 April, Law on Intellectual Property.
• Law 2/2019, of 1 March, amending the revised text of the Intellectual Property Law, approved by Royal Legislative Decree 1/1996, of 12 April, and incorporating Directive 2014/26/EU of the European Parliament and of the Council, of 26 February 2014, into Spanish law, and Directive (EU) 2017/1564 of the European Parliament and of the Council, of 13 September 2017.
• Royal Decree 311/2022, of 3 May, regulating the National Security Scheme.
• Law 34/2002, of 11 July, on Information Society Services and Electronic Commerce (LSSI).
• Law 39/2015, of 1 October, on the Common Administrative Procedure of Public Administrations.
• Law 40/2015, of 1 October, on the Legal Regime of the Public Sector.
6. Development
In order to achieve these objectives, it is necessary to:
➔ Continuously improve our information security system.
➔ Identify potential threats, as well as the impact on business operations that such threats, if they materialize, may cause.
➔ Preserve the interests of its key stakeholders (customers, shareholders, employees, and suppliers), reputation, brand, and value-creating activities.
➔ Working together with our suppliers and subcontractors to improve IT service delivery, service continuity and information security,
that have an impact on the greater efficiency of our activity.
➔ Evaluate and guarantee the technical competence of the staff, as well as ensure their adequate motivation for their participation in the continuous improvement of our processes, providing training and adequate internal communication so that they develop good practices defined in the system.
➔ Guarantee the correct condition of the facilities and the appropriate equipment, so that they are in accordance with the activity, objectives and goals of the company.
➔ Guarantee a continuous analysis of all relevant processes, establishing the relevant improvements in each case, based on the results obtained and the established objectives.
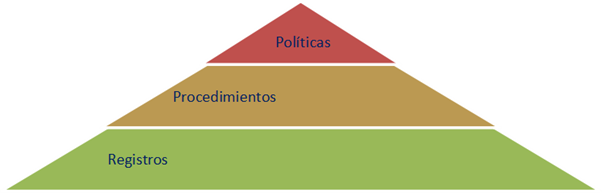
➔ Structure our management system in a way that is easy to understand. Our management system has the following structure:
The management of our system is entrusted to the Security Manager and the system will be available in our information system in a repository, which can be accessed according to the access profiles granted according to our current access management procedure.
7. Security Organization
The main responsibility lies with the General Management of Asseco Spain S.A., as it is responsible for organising the functions and responsibilities and providing adequate resources to achieve the objectives of the ENS. Managers are also responsible for setting a good example by following established safety standards.
These principles are assumed by the Management, which provides the necessary means and provides its employees with sufficient resources to comply with them, embodying and making them publicly known through these Security Policies
The defined security roles or functions are:
| Function | Duties and responsibilities |
| Responsible for the information (RINFO) | · Make decisions regarding the information processed |
| Responsible for the services (RSER) | · Coordinate the implementation of the system · Continuously improve the system |
| Responsible fo the (RSEG) | · Determining the adequacy of technical measures · Providing the best technology for service |
| Responsible for the system (RSIS) | · Coordinate the implementation of the system · Continuously improve the system |
| Address | · Provide the necessary resources for the system · Leading the system |
This definition of duties and responsibilities is completed in the job profiles and in the documents of the Register of Managers, Roles and Responsibilities system.
CONFLICT RESOLUTION
Any differences in criteria that could lead to a conflict will be dealt with within the Security Committee and the criteria of the General Directorate will prevail in all cases.
8. Safety Committee
The procedure for its appointment and renewal will be ratification in the security committee.
The Security Management and Coordination Committee is the body with the greatest responsibility within the information security management system, so all major security-related decisions are agreed upon by this committee.
The members of the information security committee are:
■ Information Controller
■ Responsible for Services
■ Safety Officer
■ System Manager
■ Company Address
These members are appointed by the committee, which alone can appoint, renew and dismiss them.
The safety committee is an autonomous, executive body with autonomy for decision-making and that does not have to subordinate its activity to any other element of our company.
Asseco Spain S.A. of Information Security is developed in the complementary document to this Security Organization Policy
This policy is complemented by the rest of the policies, procedures and documents in force to develop our management system.
9. Risk Management
All systems subject to this Policy shall conduct a risk analysis, assessing the threats and risks to which they are exposed. This analysis is reviewed regularly:
• at least once a year;
• when the information handled changes;
• when the services provided change;
• when a serious security incident occurs;
• when serious vulnerabilities are reported.
For the harmonisation of risk analyses, the ICT Security Committee will establish a reference assessment for the different types of information handled and the different services provided. The ICT Security Committee will boost the availability of resources to meet the security needs of the different systems, promoting horizontal investments.
To carry out the risk analysis, the risk analysis methodology developed in the Risk Analysis procedure will be taken into account.
10. Personnel Management
All members of Asseco Spain S.A. have the obligation to know and comply with this Information Security Policy and the Security Regulations, and it is the responsibility of the ICT Security Committee to provide the necessary means for the information to reach those affected.
All members of Asseco Spain S.A. will attend an ICT security awareness session at least once a year. A continuous awareness programme will be established to serve all members of Asseco Spain S.A., in particular those who have joined the company.
Persons with responsibility for the use, operation or administration of ICT systems shall be trained in the safe handling of the systems to the extent that they need it to carry out their work. Training will be mandatory before assuming a responsibility, whether it is your first assignment or if it is a change of job or responsibilities in it.
11. Professionalism and security of human resources
This Policy applies to all Asseco Spain S.A. personnel and external personnel who perform tasks within the company.
HR will include information security features in employee job descriptions, inform all personnel it engages of its obligations with respect to compliance with the Information Security Policy, manage Confidentiality Commitments with staff, and coordinate user training tasks with respect to this Policy.
■ The Security Management Officer (RGS) is responsible for monitoring, documenting, and analyzing reported security incidents, as well as communicating to the Information Security Committee and information owners.
■ The Information Security Committee will be responsible for implementing the necessary means and channels for the Security Management Officer (RGS) to handle reports of incidents and anomalies of the system. The Committee will also be aware of, overseeing the investigation, monitoring the evolution of information and promoting the resolution of information security incidents.
■ The Safety Management Officer (RGS) will be involved in the preparation of the Commitment
Confidentiality Notice that will be signed by employees and third parties who perform functions in Asseco Spain S.A., in advising on the sanctions that will be applied for non-compliance with this Policy and in the treatment of information security incidents.
■ All Asseco Spain S.A. personnel are responsible for reporting information security weaknesses and incidents that are detected in a timely manner.
■ Professionalism of human resources:
■ Determine the necessary competence of the staff to carry out the work that affects Information Security.
■ It is necessary to ensure that people are competent on the basis of appropriate education, training or experience.
■ Demonstrate through documented information that the competence of the personnel in the field of Information Security is necessary.
The objectives of controlling the safety of personnel are:
■ Reduce the risks of human error, implementation of irregularities, improper use of facilities and resources, and unauthorized handling of information.
■ Explain the safety responsibilities in the personnel recruitment stage and include them in the agreements to be signed and verify their compliance during the performance of the employee’s tasks.
■ Ensure that users are aware of information security threats and concerns and are trained to support Asseco Spain S.A.’s Information Security Policy in the course of their normal tasks.
■ Establish confidentiality commitments with all personnel and users outside the information processing facilities.
■ Establish the necessary tools and mechanisms to promote the communication of existing security weaknesses, as well as incidents, in order to minimise their effects and prevent their recurrence.
12. Authorization and control of access to Information Systems
The control of access to information systems aims to:
■ Prevent unauthorized access to information systems, databases, and information services.
■ Implement security in user access through authentication techniques and
authorization.
■ To control the security of the connection between the Asseco Spain S.A. network and other public or private networks.
■ Review critical events and activities carried out by users on systems.
■ Raise awareness of their responsibility for the use of passwords and equipment.
■ Ensure information security when using laptops and personal computers for remote work.
13. Facility protection
The objectives of this policy on the protection of facilities are:
To prevent unauthorized access, damage and interference to the headquarters, facilities and information of Asseco Spain S.A.
■ Protect Asseco Spain S.A.’s critical information processing equipment, placing it in protected areas and protected by a defined security perimeter, with appropriate security measures and access controls. Likewise, to contemplate the protection of this in its transfer and to remain outside the protected areas, for maintenance or other reasons.
■ Control the environmental factors that could impair the proper functioning of the computer equipment that houses the information of Asseco Spain S.A.
■ Implement measures to protect the information handled by the staff in the offices, within the normal framework of their usual tasks.
■ Provide protection proportionate to the risks identified.
This Policy applies to all physical resources related to Asseco Spain S.A.’s information systems, facilities, equipment, wiring, files, storage media, etc.
It should be noted that in the case of Asseco Spain S.A., all development environments, quality, etc., are located externally in secure hosting, so it is only the laptops and peripherals that must be protected locally.
The Security Management Officer (RGS), together with the Information Subjects, as appropriate, shall define the physical and environmental security measures for the protection of critical assets, based on a risk analysis, and shall monitor their implementation. It will also verify compliance with physical and environmental security provisions.
The heads of the different departments will define the levels of physical access of Asseco Spain S.A. personnel to the restricted areas under their responsibility. The Information Owners will formally authorize off-site work with information about their business to employees of Asseco Spain S.A. when they deem it appropriate.
All Asseco Spain S.A. staff are responsible for compliance with the clean screen and desktop policy, for the protection of information related to daily work in the offices.
14. Product Procurement
Different departments must ensure that ICT security is an integral part of every stage of the system’s lifecycle, from conception to decommissioning, development or acquisition decisions and operational activities. Security requirements and funding needs should be identified and included in planning, in the request for proposals, and in tender documents for ICT projects.
On the other hand, information security will be taken into account in the acquisition and maintenance of information systems, limiting and managing change.
15. Security by default
Asseco Spain S.A. considers it strategic for the entity that the processes integrate information security as part of its life cycle. Information systems and services must include security by default from their creation to their retirement, including security in development and/or acquisition decisions and in all operating activities, establishing security as an integral and transversal process.
16. System integrity and updating.
Asseco Spain S.A. is committed to guaranteeing the integrity of the system through a change management process that allows the control of the updating of the physical or logical elements through the authorization prior to their installation in the system. This assessment will be carried out mainly by the technical management who will assess the impact on the security of the system before making the changes and will monitor in a documented way those changes that are assessed as important or with implications for the security of the systems.
Periodic security reviews will assess the security status of the systems, in relation to the manufacturers’ specifications, vulnerabilities and to updates that affect them, reacting diligently to manage the risk in view of their security status.
17. Protecting Information in Transit and Stored
Asseco Spain S.A. establishes protection measures for the Security of Information stored or in transit through insecure environments. Laptops, peripheral devices, information carriers and communications over open networks or with weak encryption will be considered insecure environments.
18. Prevention of interconnected information systems
Asseco Spain S.A., establishes protection measures for Information Security especially to protect the perimeter, in particular, if it connects to public networks, especially if they are used in whole or mainly, for the provision of electronic communications services available to the public.
In any case, the risks arising from the interconnection of the system, through networks, with other systems will be analysed, and their point of connection will be controlled. Electronic connections available to the public.
19. Activity logs
Asseco Spain S.A. will record the activities of users, retaining the information necessary to monitor, analyze, investigate and document improper or unauthorized activities, allowing the identification of the person acting at all times.
The main objectives of Incident Management are to:
• Establish a system for detecting and reacting to harmful code.
• Have procedures for managing security incidents and weaknesses detected in the elements of the information system.
• These procedures will cover detection mechanisms, classification criteria, analysis and resolution procedures, as well as channels of communication to interested parties and the recording of actions.
• This register is used for continuous improvement of system security.
• Ensure that IT services return to optimal performance.
• Reduce the possible risks and impacts that the incident may cause.
• Ensure the integrity of systems in the event of a security incident.
• Communicate the impact of an incident as soon as it is detected to trigger the alarm; and implement an appropriate business communication plan.
• Promote business efficiency.
20. Business continuity
Asseco Spain S.A., with the aim of guaranteeing the continuity of activities, establishes measures so that the systems have backup copies and establishes the necessary mechanisms to guarantee the continuity of operations, in the event of loss of the usual means of work.
21. Continuous improvement of the security process
Asseco Spain S.A. establishes a process of continuous improvement of information security by applying the criteria and methodology established in the National Security Scheme.
In Madrid, February 5, 2026
General Directorate


























